Enable VMware Fault Tolerance in nested enviroments
While playing around in my lab, I wanted to enable VMware Fault Tolerance (FT) for a VM. In the absence of physical HW I use a nested enviroment, which is running on a HP ProLiant DL160 G6 (2x Intel Xeon E5520, 32G RAM, a RAID 0 with 4 SATA drives). FT isn’t available in nested enviroments, because HW virtualization features are required. This screenshot was taken from the web client.
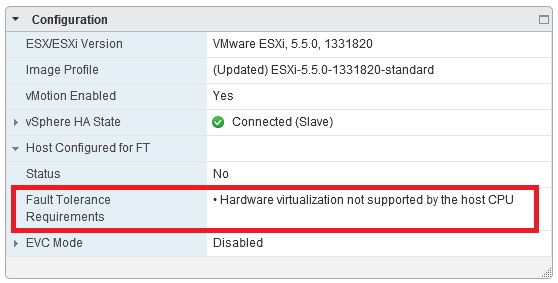
Patrick Terlisten/ vcloudnine.de/ Creative Commons CC0
But “isn’t available” doesn’t mean that you can’t enable it. ;) As always this isn’t supported by VMware. It’s for lab enviroments, trainings etc., but not for production. You have to set three configuration parameters for the VM that you want to use with FT. If you use the web client, you can set the configuration parameters as follows:
Edit Settings… > VM Options > Advanced > Edit Configuration…
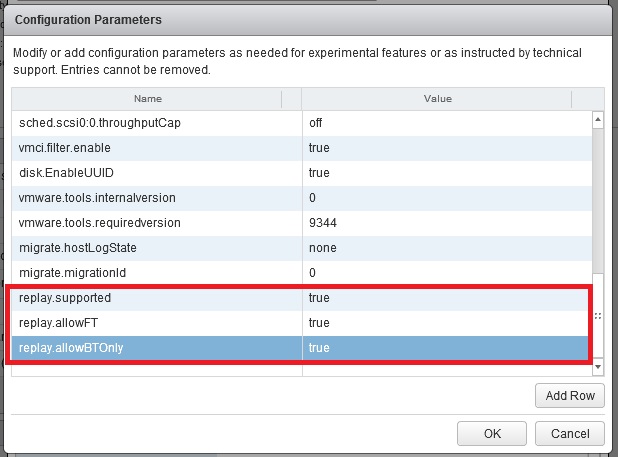
Patrick Terlisten/ vcloudnine.de/ Creative Commons CC0
For easy copy ’n paste here the parameters:
replay.supported = "true"
replay.allowFT = "true"
replay.allowBTOnly = "true"
After setting the parameters you can enable FT and start the VM.
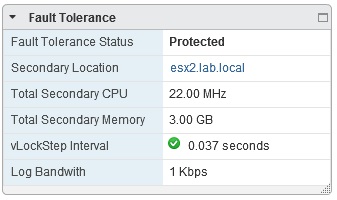
Patrick Terlisten/ vcloudnine.de/ Creative Commons CC0
Please note that you can only run 32-bit guests! This is due to the binary translation (replay.allowBTOnly). A FT-secured 64-bit Windows 2008 R2 won’t be possible. But to show the configuration and use of FT a 32-bit Windows 2003 should be sufficient. :) I have configured FT in my lab and I took the screenshots from the vSphere 5.5 Web Client. I use VM HW 9 for the nested ESXi and VHV is enabled in the CPU section. If you are searching for more: virtuallyGhetto is an awesome source, especially for nested virtualization and everything around automation using various API/ SDK and CLI. Kudos to William Lam for the work he puts in there.
