Mail notification for specific Active Directory security events
A customer used PRTG Network Monitor to notify him in case of account lockouts. This worked quite well until we implemented Admin Tiering. In order to get a mail notification in case of an account lockout, or other security-relevant events in Active Directory, I customized some scripts from my PowerShell dump.
The solution is pretty simple: I used the Task Planner to run a PowerShell script if a specific event id occurs. The events are generated in case of a various number of Active Directory events. You have to enable audit policy to get the needed events in the security event log. Take a look at Microsoft audit policy recommendations and enable what you need. I recommend to enable the stronger settings.
I implemented five scripts:
- Account lockout
- New account in Active Directory
- New member in domain-local group
- New member in domain-global group
- New member in universal group
The implementation is pretty easy. Create a basic task and execute this task if a specific event occurs.
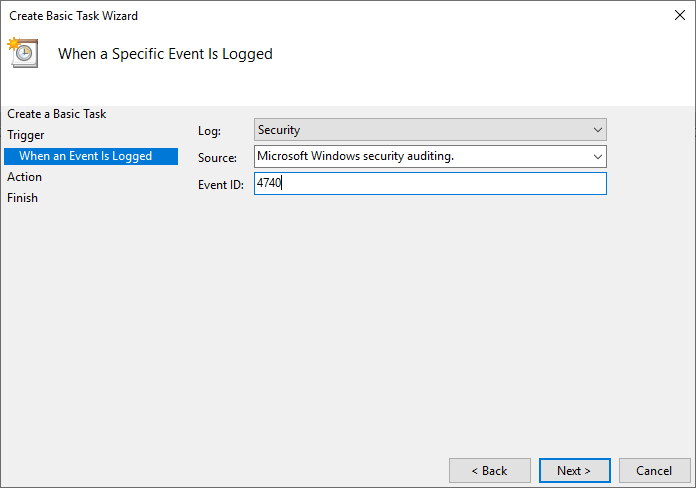
Patrick Terlisten/ vcloudnine.de/ Creative Commons CC0
The action is “Start a program”, like in the following screenshot.
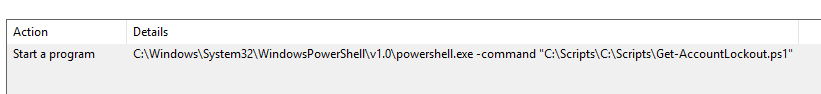
Patrick Terlisten/ vcloudnine.de/ Creative Commons CC0
Save the task and then change the user, which is used to run this task, to SYSTEM.
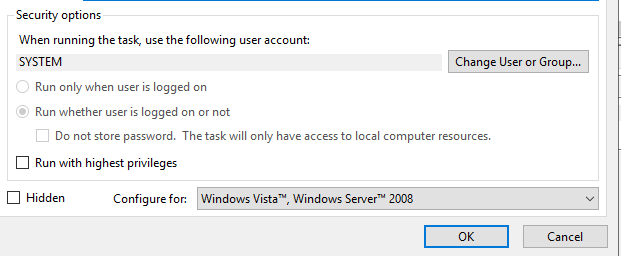
Patrick Terlisten/ vcloudnine.de/ Creative Commons CC0
Please note, that you run these scripts with SYSTEM privileges. So make sure that NO ONE can easily edit these scripts! Best way is to restrict it to specific domain admins, restrict access to your domain controllers etc!
Repeat these steps for each script and implement them on each domain controller.
Please leave a comment with feedback :)
